wordpress updates & maintenance
Specializing in content updates and wordpress maintenance for corporate and small business websites.
Call on us when you need something done on your website, whether its a quick update or a major change.
Phone
647 243 4688
Website Updates
Need a website update? Text, images, pages, or even a system check/update?
No problem, that’s what we do! One time or many time Wordpress website updates not attached to a plan.
Maintenance Plans
Keep your website safe and secure with a proactive maintenance plan and rely on us for your content updates?
Check out our Wordpress website maintenance and care plans.
Fix My Website
Is something not working with your Wordpress site? Pages not displaying, too slow, hacked?
A terrific platform, Wordpress does have a lot of moving parts. Let’s fix it.
Wordfence Security
Wordfence Intelligence Weekly WordPress Vulnerability Report (February 5, 2024 to February 11, 2024)
Did you know we’re running a Bug Bounty Extravaganza again? Earn over 6x our usual bounty rates, up to $10,000, for all vulnerabilities submitted...
2023’s Critical WordPress Vulnerabilities and How They Work
Did you know we’re running a Bug Bounty Extravaganza again? Earn over 6x our usual bounty rates, up to $10,000, for all vulnerabilities submitted...
Wordfence Intelligence Weekly WordPress Vulnerability Report (January 29, 2024 to February 4, 2024)
Did you know we’re running a Bug Bounty Extravaganza again? Earn over 6x our usual bounty rates, up to $10,000, for all vulnerabilities submitted...
INSIGHTS / Latest
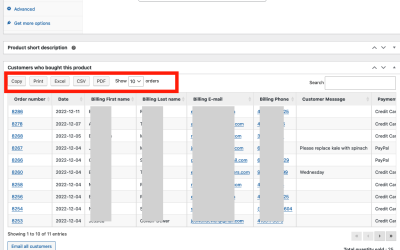
WooCommerce: 2 Ways to Find Customers who Bought a Specific Product
Sometimes you want to be able to communicate with customers who purchased a particular product. Here's two ways to find them. As you...
Divi Website Editor Training Refresher
Website training refreshers, going over everything from how to edit a page in Divi to how to process orders in Woocommerce, plus...
Investigating and Fixing a Slow Website
Recently a client reached out to us whom we hadn't heard from in a while: their website had become very slow. It wasn't just...
Is your website (still) optimized for Search Engines?
We often encounter sites that were optimized when they were first built, but nothing has been done since. Thats a lost opportunity...
How to Create Coupon Codes with your WooCommerce Online Store
Did you know that with WooCommerce you have coupon functionality built in to your online store? You're easily able to create coupon...
Have you been maintaining your websites AODA compliance?
Was your website created to be AODA compliant? Is it still compliant? Did you know that any time you make a content update to the...